1. Introduction: The Urgent Call
I was at a conference when the call came in. Timing rarely matters in the crypto world when things go wrong. On the line was a longtime friend of the firm, a seasoned crypto investor and one of our fund participants. In just minutes, a sophisticated scam had drained nearly $1 million from his digital wallets.
As we investigated, it became clear this wasn’t an isolated incident. The attack was part of a coordinated scam that had already stolen more than $7 million from multiple victims.
What follows is a behind-the-scenes look at how we at Sarson Funds tackled the situation. From the initial forensic dive to our collaboration with federal law enforcement, this walkthrough shows how we respond to complex incidents. It reflects the same investigative and protective tools we rely on to assist both clients and the broader crypto community.
2. The Attack Vector: A Deceptive App on a Trusted Platform
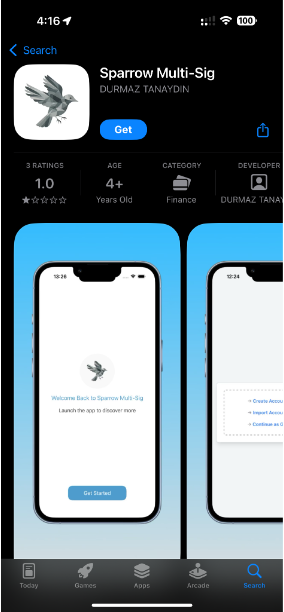
The scam began with a fake app on the Apple App Store labeled “Sparrow Multi-Sig.” It closely mimicked the real Sparrow Wallet, a well-respected desktop-only Bitcoin tool.
At first glance, the app seemed legitimate. But a closer inspection revealed its deceit. The scammers likely bypassed Apple’s crypto-related app scrutiny by mislabeling the software. Rather than presenting it as a wallet, they described it as a CRM platform:
Welcome to Sparrow Multi-Sig — a refined CRM built for teams who value simplicity, control, and trust.
Sparrow Multi-Sig combines essential CRM features with the power of multi-signature approval. Manage leads, track interactions, and collaborate securely — all in a sleek, minimal interface designed to keep you focused.
This false classification likely enabled the app to slip past Apple’s review team. Despite screenshots clearly showing a crypto wallet interface, the app was approved. The developer’s App Store page even linked to a polished external site (sparroweb.xyz, which should not be visited), further legitimizing the ruse and distinguishing it from the authentic Sparrow Wallet.
3. The Investigation: From OSINT to On-Chain Forensics
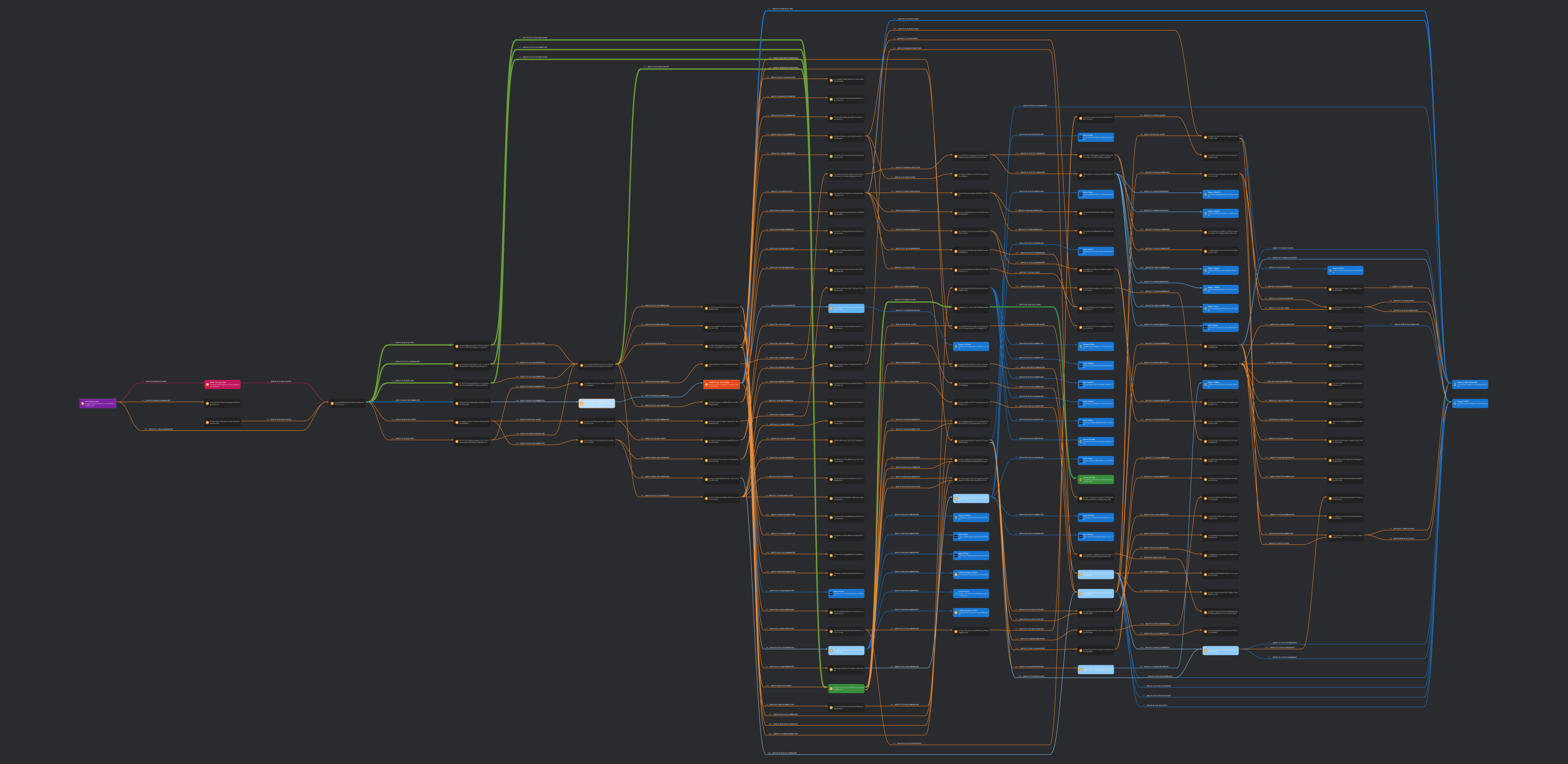
With the victim’s wallet address in hand, our team began tracking the stolen Bitcoin transactions. As soon as he entered his recovery phrase into the fake app, scripts automatically drained his wallet.
The BTC was first funneled to a consolidation wallet, then split across more than 50 addresses in an effort to obscure the trail. Using blockchain analytics, we traced these flows to deposit wallets on major centralized exchanges—potentially linking the scammers to verified identities.
We compiled a detailed map of the laundering process and shared this data with our law enforcement contacts, including the FBI. This may ultimately assist in asset recovery or identification of the attackers.
4. Connecting the Dots: Uncovering a Wider Criminal Operation
While tracing the stolen funds, we discovered a thread on X (formerly Twitter) from a user named Jimmy Ramirez. He described an identical experience involving the same fake Sparrow app. On-chain data confirmed the connection.
This breakthrough helped unite victims and led to a coordinated legal effort—culminating in the lawsuit Ramirez v. Doe et al (Case 2:25-cv-01576). The court has since approved subpoenas for Apple and Namecheap to identify the fake developer and domain registrar behind the scam.
Recognizing the scope of the fraud, we brought in respected on-chain investigator ZachXBT. His expertise in blockchain forensics helped us uncover further movement of stolen funds, which were being laundered through bridging services.
Our communications with law enforcement remained active throughout the process. Every piece of evidence, from the domain to the full transaction chain, was delivered to the FBI and local authorities.
5. Security Lessons and First Steps for Victims
This incident highlights several critical lessons:
The main error was entering a recovery phrase into an untrusted app. A recovery phrase—typically 12 or 24 words—is the master key to a crypto wallet. It should only ever be entered into a verified hardware wallet during recovery. Never submit it into a website, mobile app, or online form.
Importantly, this wasn’t just user error. It was a highly targeted social engineering attack that exploited trust in Apple and the Sparrow brand.
If you are ever targeted, take the following steps immediately:
-
- Collect All Evidence: Gather transaction IDs (TX hashes), wallet addresses, usernames, emails, chat logs, website/app links, and any other relevant data.
- File an IC3 Report: Visit the FBI’s Internet Crime Complaint Center (IC3) and submit a detailed report. Include all collected evidence, especially transaction details.
- Be Thorough: The more comprehensive your report, the better the chance your case will connect with others. This improves the odds of tracking and stopping the perpetrators.
6. Navigating Security with Trusted Partners
Incidents like this highlight how difficult it can be to manage crypto assets safely, especially as scams grow more sophisticated. Even experienced users can be misled by apps that appear legitimate on trusted platforms.
At Sarson Funds, our team has spent years operating in high-risk environments. We have built our investment infrastructure around secure practices, including hardware wallets, multi-signature approvals, and regular auditing. That experience also means we are often pulled in when cases like this unfold.
Our experience in digital asset security means we’re often called in when cases like this emerge. From working with federal law enforcement to tracing funds on-chain, we’ve developed a reputation for handling complex investigations with precision.
We’ll continue to support the victims involved and share updates as this case unfolds.
Disclosures: This article is for informational purposes only and should not be considered financial, legal, tax, or investment advice. It provides general information on cryptocurrency without accounting for individual circumstances. Sarson Funds, Inc. does not offer legal, tax, or accounting advice. Readers should consult qualified professionals before making any financial decisions. Cryptocurrency investments are volatile and carry significant risk, including potential loss of principal. Past performance is not indicative of future results. The views expressed are those of the author and do not necessarily reflect those of Sarson Funds, Inc. By using this information, you agree that Sarson Funds, Inc. is not liable for any losses or damages resulting from its use.